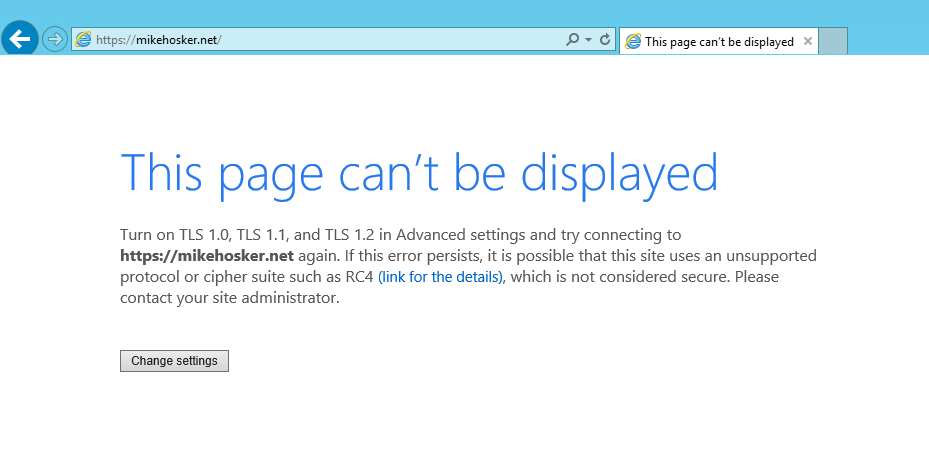
Strange Internet Explorer TLS Error
A freshly built VM was displaying TLS error pages in Internet Explorer when accessing sites like https://portal.office.com, despite those sites being whitelisted in Azure Firewall and the firewall logs showing allows (not denies).
Network captures showed no firewall issues. The problem only affected this one machine, which made misconfiguration seem unlikely. After extensive troubleshooting, Microsoft support identified the root cause: SCHANNEL protocol configuration.
The Fix
The resolution involved modifying registry keys under:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols
Changes required
Disable SSL 2.0 and SSL 3.0 (Server subkeys):
SCHANNEL\Protocols\SSL 2.0\Server
Enabled = 0
DisabledByDefault = 1
SCHANNEL\Protocols\SSL 3.0\Server
Enabled = 0
DisabledByDefault = 1
Enable TLS 1.0, 1.1, and 1.2 — and critically, remove the DisabledByDefault flags from TLS 1.1 and 1.2:
SCHANNEL\Protocols\TLS 1.0\Client
Enabled = 1
DisabledByDefault = 0
SCHANNEL\Protocols\TLS 1.1\Client
Enabled = 1
DisabledByDefault = 0
SCHANNEL\Protocols\TLS 1.2\Client
Enabled = 1
DisabledByDefault = 0
After applying the registry changes and rebooting, access was restored.
Key Takeaway
Always back up the parent registry key before making SCHANNEL changes:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL
Right-click → Export to save a .reg backup you can restore if something goes wrong.
The lesson here is that what looks like a network or firewall problem can turn out to be a protocol configuration issue. If firewall logs show allows but TLS errors persist, SCHANNEL is worth investigating — especially on freshly provisioned or migrated VMs where the protocol registry keys may have been set to non-defaults.